Framework curbs agentic LLM risks in enterprise SOC
Enterprise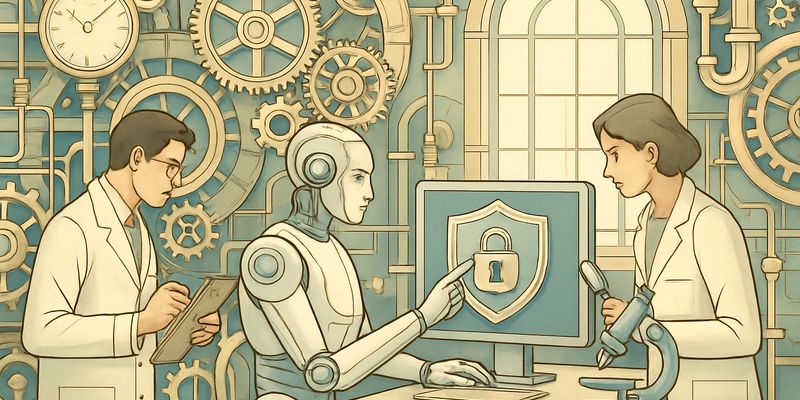
Enterprises are piloting agentic systems built on Large Language Models (LLMs) to triage alerts, pull logs and even draft remediation steps. That autonomy is the draw, but it also opens doors traditional, deterministic pipelines simply did not have. A new framework, AgenticCyOps, tries to make those doors visible and lockable before attackers walk through them.
The authors take a step back from prompt-level exploits and map risks across three layers: component, coordination and protocol. Their key finding is pragmatic. Across published attack vectors, the same two integration surfaces keep recurring: tool orchestration and memory management. Treat those as primary trust boundaries and you can concentrate controls where it matters.
What the framework adds
The paper proposes five defensive principles that align with established standards such as NIST, ISO 27001, GDPR and the EU AI Act: authorised interfaces, capability scoping, verified execution, memory integrity and synchronization, and access-controlled data isolation. In plain terms: authenticate which agent can invoke which tool, scope what it can do, verify execution before effects take place, protect and reconcile memory, and isolate data access by design.
They instantiate the approach in a Security Operations Centre (SOC) workflow using the Model Context Protocol (MCP). A central Host orchestrator mediates communication, while phase-scoped agents handle Monitor, Analyse, Admin and Report functions. A Memory Management Agent enforces organisational memory boundaries. The system uses signed manifests, runtime scoping, consensus validation loops and write-boundary filtering to provide defence in depth.
On paper, this structure intercepts three of four representative attack chains within the first two steps and cuts exploitable trust boundaries by at least 72% compared with a flat multi-agent system (from 200 to 56). Each documented vector is covered by at least two of the principles. The evaluation uses coverage mapping, attack-path tracing and boundary counting rather than live adversarial testing.
What to watch
No architecture is free. A Host-centric design introduces a single point of failure. Verify-first and consensus loops add latency that could bite in time-critical response. Validators and policy repositories become tempting targets. The framework does not solve cross-organisation ingestion validation, and there is no standard lifecycle for agent credentials. Runtime overheads and scalability remain unmeasured.
Even so, the policy alignment is useful. Mapping controls to NIST and ISO 27001 helps with auditability and procurement. GDPR and EU AI Act references point to a world where agent capabilities, data access and logging need to be reasoned about up front, not bolted on later. That is the sort of governance that can keep experimentation on the right side of risk.
For teams exploring agentic SOC workflows, the paper supports a few near-term moves:
- Treat tool orchestration as a privileged boundary; enforce authenticated, scoped interfaces and verify sensitive actions.
- Separate and govern memory: integrity checks, synchronisation rules and access-controlled, per-organisation stores.
- Adopt a Host-mediated pattern (MCP or similar) with phase-scoped agents and consensus validation for critical steps.
The field still needs adversarial validation, latency profiling and benchmarks for multi-agent security. But as a blueprint that links engineering practice to compliance expectations, AgenticCyOps is a solid nudge towards safer, more governable LLM agents in the SOC.
Additional analysis of the original ArXiv paper
📋 Original Paper Title and Abstract
AgenticCyOps: Securing Multi-Agentic AI Integration in Enterprise Cyber Operations
🔍 ShortSpan Analysis of the Paper
Problem
The paper studies security risks introduced when large language model driven multi-agent systems are granted autonomous control of tools, shared memory and communications in enterprise cyber operations. It argues that prior work focuses on prompt-level exploits and isolated vectors but lacks a holistic architectural threat model for enterprise deployments. In adversarial domains such as cybersecurity operations, compromised agents can actively subvert detection and response, so systematic mitigation of integration-level attack surfaces is essential.
Approach
The authors decompose multi-agent system threats across three abstraction layers: component, coordination and protocol. They identify two recurring, exploitable integration surfaces: tool orchestration and memory management, and treat these as primary trust boundaries. From that decomposition they derive five defensive principles: authorised interfaces, capability scoping, verified execution, memory integrity and synchronization, and access-controlled data isolation. The framework is instantiated in a Security Operations Centre workflow using the Model Context Protocol as the structural basis, with a central Host orchestrator, phase-scoped agents for Monitor, Analyse, Admin and Report, consensus-based validation loops, and a dedicated Memory Management Agent enforcing organisational memory boundaries. Evaluation uses coverage mapping, attack-path tracing and trust-boundary counting against a flat multi-agent baseline.
Key Findings
- The systematic decomposition shows that diverse documented attack vectors converge on two integration surfaces: tool orchestration and memory management, motivating focused trust boundaries.
- The five defensive principles map to the agent-tool lifecycle (authenticate, scope, verify) and memory dimensions (integrity, access control), providing complementary coverage so that each vector is mitigated by at least two principles.
- Applied to a SOAR-style CyberOps architecture, the design intercepts three of four representative multi-step attack chains within the first two steps and enforces defence-in-depth via signed manifests, runtime scoping, consensus validation and write-boundary filtering.
- Trust-boundary analysis shows a minimum 72% reduction in exploitable boundaries (from 200 to 56) compared with a flat MAS by using phase-scoping, Host-mediated communication and Memory Management Agent arbitration; retained boundaries are subject to active verification.
Limitations
The proposed vertical Host-centric architecture introduces a central point of failure and may not cover federated resilience without further work. The verify-first paradigm can add latency that may be problematic for time-critical actions. Consensus validators and policy repositories themselves can become attack surfaces if compromised. The framework does not resolve cross-organisation ingestion validation and lacks a standardised agent credential lifecycle; the evaluation is structural rather than adversarial or empirical, and runtime overheads and scalability are unmeasured.
Why It Matters
AgenticCyOps offers a practical architecture and set of principles to reduce systemic risk when integrating agentic AI into enterprise CyberOps. By turning tool orchestration and memory management into enforced trust boundaries, the framework enables defence-in-depth, clearer auditability and measurable reductions in exploitable interfaces. For security professionals, the work supplies an actionable mapping from threats to architectural controls and highlights open research needs such as adversarial validation of consensus, latency profiling, benchmarks for multi-agent security and mechanisms for long-running agent authorisation.